OpenSSH : SSH Key-Pair Authentication2024/04/26 |
|
Configure SSH server to login with Key-Pair Authentication.
Create a private key for client and a public key for server to do it. |
|
| [1] | Create Key-Pair by each user, so login with a common user on SSH Server Host and work like follows. |
|
# create key-pair ubuntu@dlp:~$ ssh-keygen Generating public/private ed25519 key pair. Enter file in which to save the key (/home/ubuntu/.ssh/id_ed25519): # Enter or input changes if you want Enter passphrase (empty for no passphrase): # set passphrase (if set no passphrase, Enter with empty) Enter same passphrase again: Your identification has been saved in /home/ubuntu/.ssh/id_ed25519 Your public key has been saved in /home/ubuntu/.ssh/id_ed25519.pub The key fingerprint is: SHA256:VPFjxEDeLKJLbKQurhgh0VIZxIrq8K+C+fg1iow8PmY ubuntu@dlp.srv.world The key's randomart image is: ..... .....ubuntu@dlp:~$ ll ~/.ssh total 24 drwx------ 2 ubuntu ubuntu 4096 Apr 26 06:47 ./ drwxr-x--- 4 ubuntu ubuntu 4096 Apr 26 06:45 ../ -rw------- 1 ubuntu ubuntu 0 Apr 26 01:09 authorized_keys -rw------- 1 ubuntu ubuntu 464 Apr 26 06:47 id_ed25519 -rw-r--r-- 1 ubuntu ubuntu 102 Apr 26 06:47 id_ed25519.pub -rw------- 1 ubuntu ubuntu 978 Apr 26 06:28 known_hosts -rw-r--r-- 1 ubuntu ubuntu 142 Apr 26 06:28 known_hosts.oldubuntu@dlp:~$ cat ~/.ssh/id_ed25519.pub >> ~/.ssh/authorized_keys |
| [2] | Transfer the private key created on the Server to a Client, then it's possible to login with Key-Pair authentication. |
|
# transfer the private key to the local ssh directory ubuntu@node01:~$ scp ubuntu@10.0.0.30:/home/ubuntu/.ssh/id_ed25519 ~/.ssh/ ubuntu@10.0.0.30's password: id_rsa 100% 2655 1.8MB/s 00:00ubuntu@node01:~$ ssh ubuntu@10.0.0.30 Enter passphrase for key '/home/ubuntu/.ssh/id_ed25519': # passphrase if you set Welcome to Ubuntu 24.04 LTS (GNU/Linux 6.8.0-31-generic x86_64) ..... ..... ubuntu@dlp:~$ # logined |
| [3] | If you set [PasswordAuthentication no], it's more secure. |
|
root@dlp:~#
vi /etc/ssh/sshd_config # line 57 : uncomment and change to [no] PasswordAuthentication no
# line 62 : make sure the setting below KbdInteractiveAuthentication no # If the following file exists, # change the content in the same way or delete the file itself root@dlp:~# cat /etc/ssh/sshd_config.d/50-cloud-init.conf PasswordAuthentication yes root@dlp:~# rm /etc/ssh/sshd_config.d/50-cloud-init.conf systemctl restart ssh |
|
SSH Key-Pair Authentication on Windows Client #1
|
|
This is the example to login to SSH server from Windows Client.
On this example, it shows with Putty. Before it, Transfer a private key to Windows client computer. |
|
| [4] |
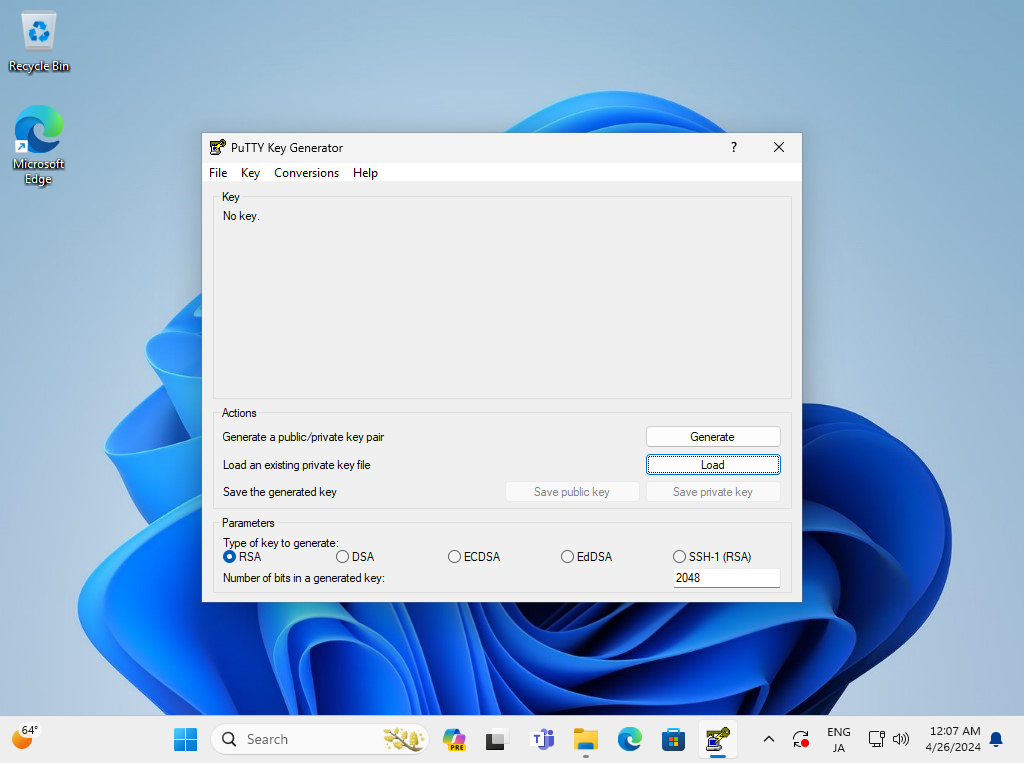
Run [Puttygen.exe] that is included in [Putty]. (placed in the folder [Putty.exe] is also placed) If not included, Download it from official site (www.chiark.greenend.org.uk/~sgtatham/putty/). After starting [Puttygen.exe], Click [Load] button on the following window. |
|
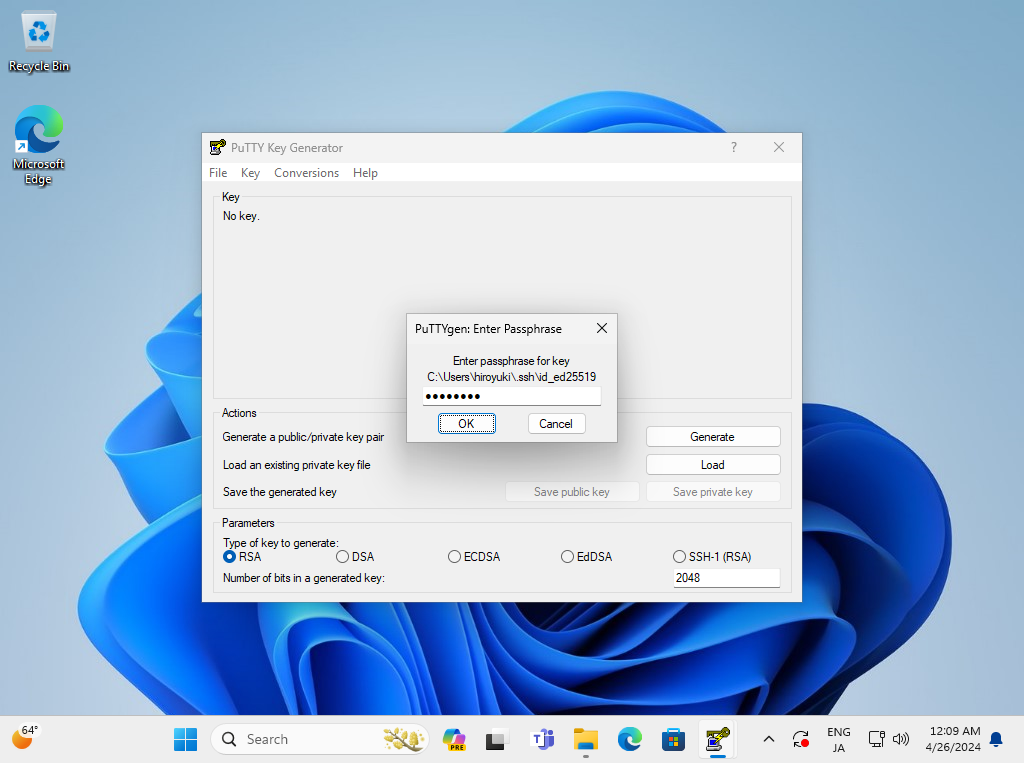
| [5] | Specify the private key that you transferred from SSH server, then passphrase is required like follows, answer it. (if not set passphrase, this step is skipped) |
|
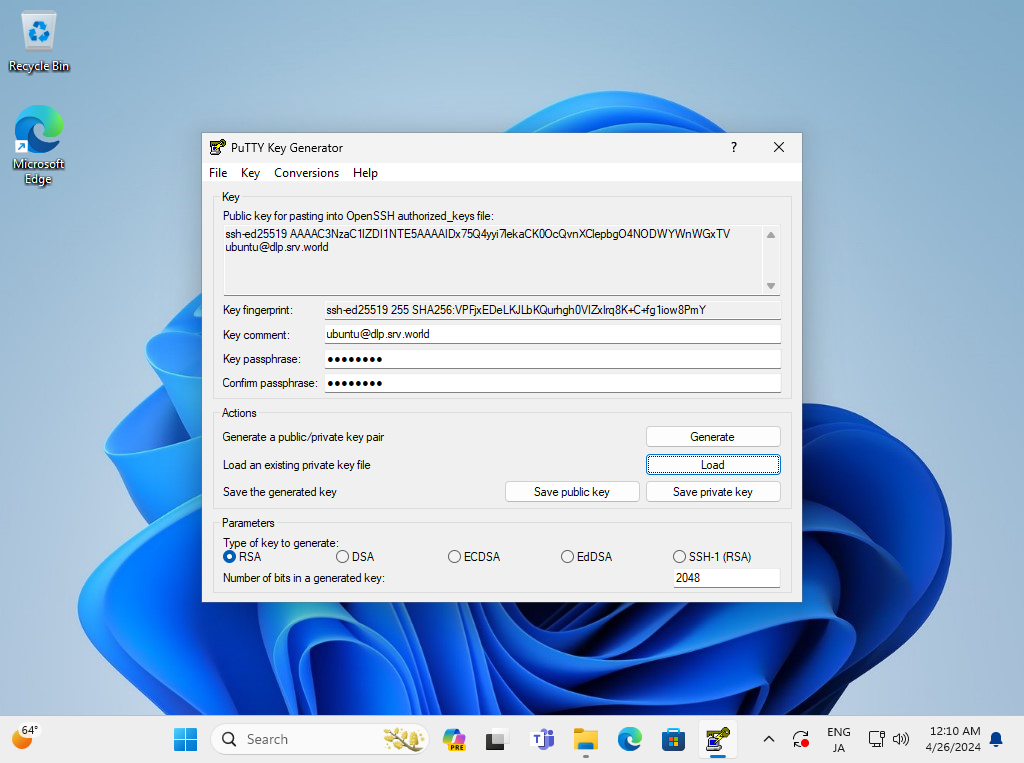
| [6] | Click [Save private key] button to save it under a folder you like with any file name you like. |
|
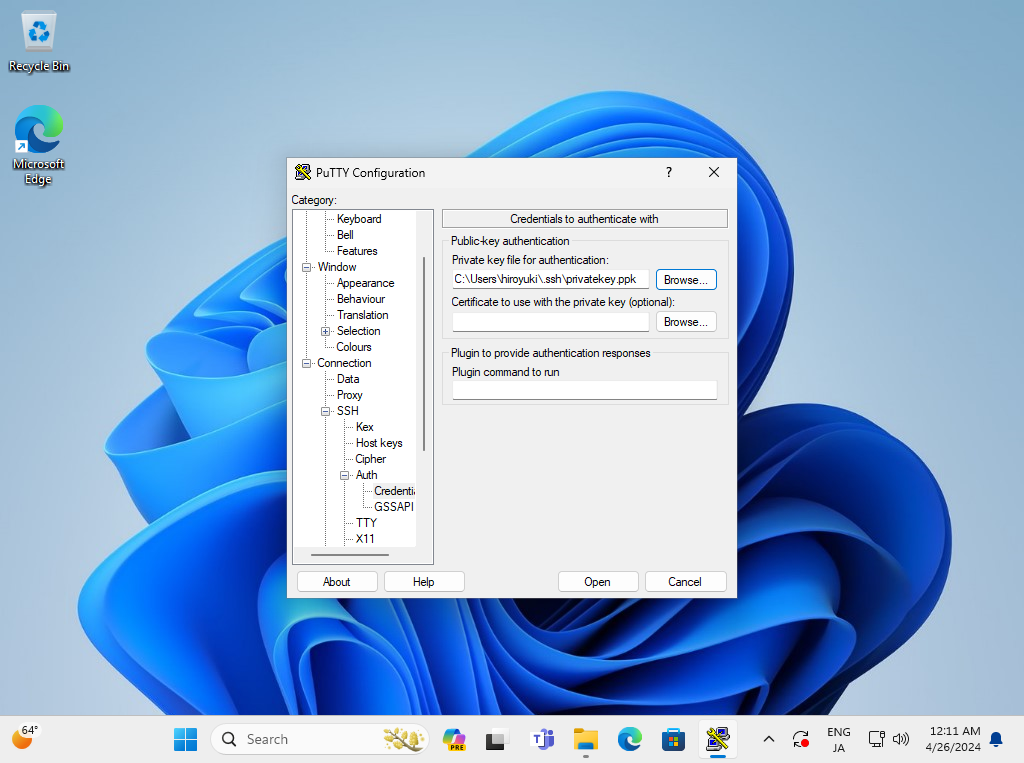
| [7] | Start Putty and Open [Connection] - [SSH] - [Auth] - [Credentials] on the left pane, then specify your private key on the [Private key file] field. |
|
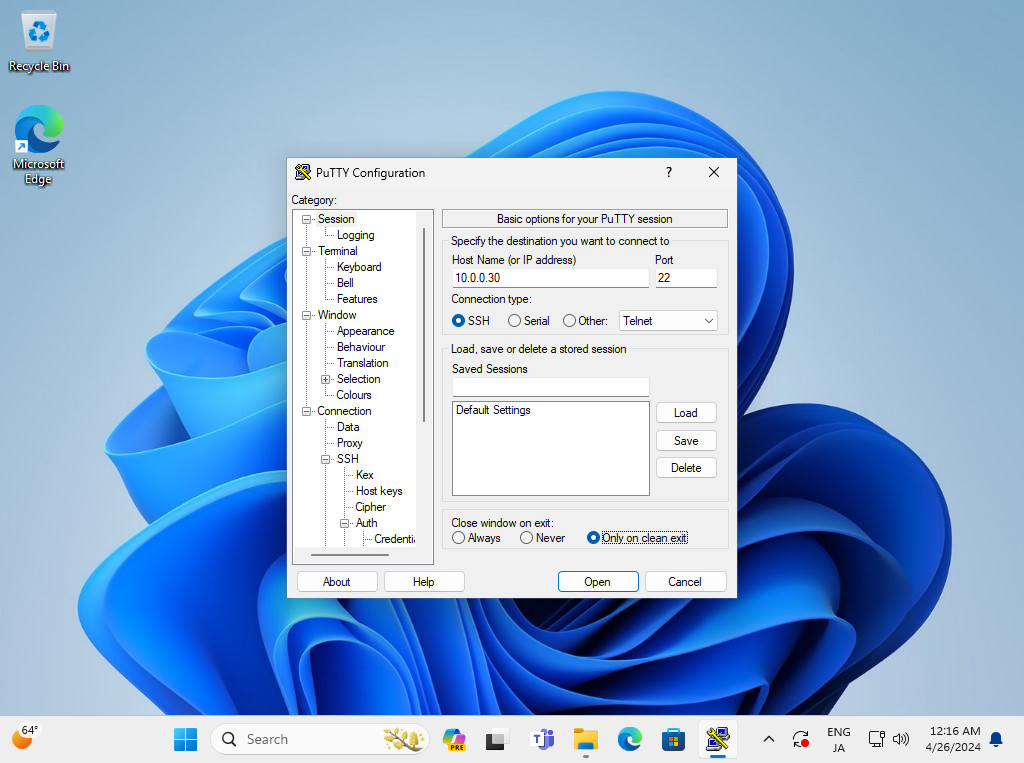
| [8] | Back to the [Session] on the left pane and specify your SSH server host to Connect. |
|
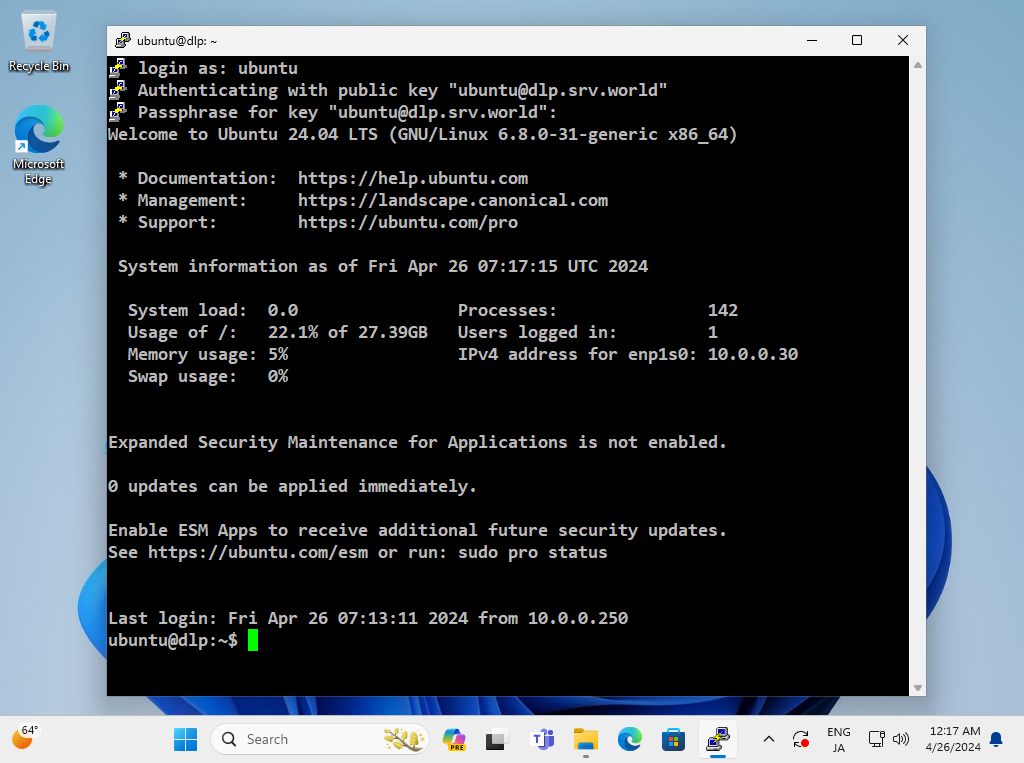
| [9] | When SSH key-pair is set, the passphrase if it is set is required to login like follows, then answer it. |
|
|
SSH Key-Pair Authentication on Windows #2
|
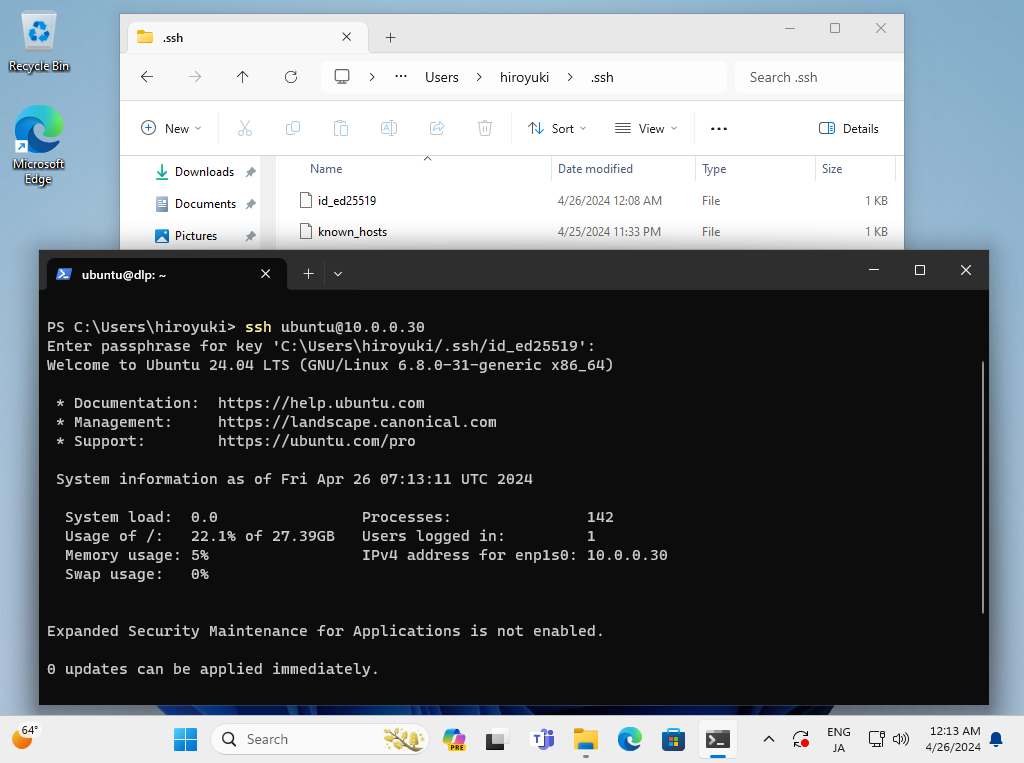
| [10] | OpenSSH Client has been implemented as an Windows feature, so it's possible to authenticate with SSH Key-Pair without Putty and other 3rd party softwares. Transfer your private key to your Windows and put it under the [(logon user home).ssh] folder like follows, then it's ready to use Key-Pair authentication. |
|
Matched Content