Apache2 : Configure mod_md2022/05/10 |
|
Install and Configure [mod_md] to automate managing certificates from Let's Encrypt.
It's possible to configure for each VirtualHost.
And it's not need to configure manual SSL/TLS setting like here for the Site with [mod_md].
Also it needs that it's possible to access from the Internet to the Site with [mod_md] because of verification from Let's Encrypt.
|
|
| [1] | Install [mod_md]. |
|
root@www:~# apt -y install libapache2-mod-md
|
| [2] | Configure [mod_md]. |
|
root@www:~#
vi /etc/apache2/conf-available/acme.conf # create new
MDBaseServer on
MDCertificateProtocol ACME
MDCAChallenges http-01
MDDriveMode auto
MDPrivateKeys RSA 2048
MDRenewWindow 33%
MDStoreDir md
MDCertificateAuthority https://acme-v02.api.letsencrypt.org/directory
MDCertificateAgreement https://letsencrypt.org/documents/LE-SA-v1.2-November-15-2017.pdf
<Location "/md-status">
SetHandler md-status
Require ip 127.0.0.1 10.0.0.0/24
</Location>
# [MDRenewWindow]
# default is [33%] if not specified
# if validity of certificates falls specified duration,
# [mod_md] will get new certificates
# 90 days * 33% ≒ 30 days
# if you'd like to set with day, specify [d]
# 30 days ⇒ [30d]
# [MDStoreDir]
# the directory certificates or other data are stored
# if not specified, default is [md]
# it is relative path from [ServerRoot] in [httpd.conf]
# [md-status]
# monitor MD status
|
| [3] | Configure each VirtualHost you'd like to set [mod_md]. It needs to specify valid email address for each [ServerAdmin] directive because Let's Encrypt will send various notification. |
|
# for example, set on the site [rx-9.srv.world] site root@www:~# vi /etc/apache2/sites-available/rx-9.srv.world.conf
MDomain rx-9.srv.world
MDCertificateAgreement accepted
DirectoryIndex index.html
ServerAdmin root@rx-9.srv.world
<VirtualHost *:80>
DocumentRoot /var/www/rx-9
ServerName rx-9.srv.world
</VirtualHost>
<VirtualHost *:443>
SSLEngine on
DocumentRoot /var/www/rx-9
ServerName rx-9.srv.world
</VirtualHost>
a2enmod md Enabling module md. To activate the new configuration, you need to run: systemctl restart apache2root@www:~# a2enconf acme Enabling conf acme. To activate the new configuration, you need to run: systemctl reload apache2root@www:~# a2ensite rx-9.srv.world Enabling site rx-9.srv.world. To activate the new configuration, you need to run: systemctl reload apache2
root@www:~#
systemctl restart apache2
# on initial loading, some validation checks run and # dumy certificate is created under the directory you set for [MDStoreDir] root@www:~# ll /etc/apache2/md/domains/rx-9.srv.world total 20 drwx------ 2 root root 4096 May 10 05:13 ./ drwx------ 3 root root 4096 May 10 05:13 ../ -rw------- 1 root root 1704 May 10 05:13 fallback-privkey.pem -rw------- 1 root root 1168 May 10 05:13 fallback-pubcert.pem -rw------- 1 root root 581 May 10 05:13 md.json # if all checks passed, valid certificate is gotten root@www:~# ll /etc/apache2/md/domains/rx-9.srv.world total 32 drwx------ 2 root root 4096 May 10 05:14 ./ drwx------ 3 root root 4096 May 10 05:14 ../ -rw------- 1 root root 4895 May 10 05:14 job.json -rw------- 1 root root 578 May 10 05:14 md.json -rw------- 1 root root 1704 May 10 05:14 privkey.pem -rw------- 1 root root 5591 May 10 05:14 pubcert.pem |
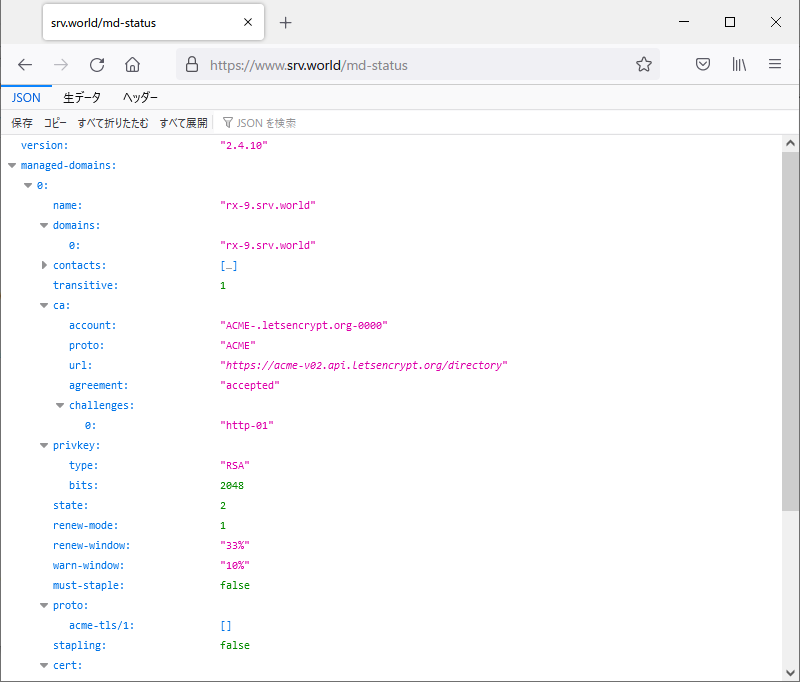
| [4] | It's possible to confirm expiration date and others of certificate with [openssl] command like follows. Or it's possible to see them to access to the URL of [md-status] you set on [2]. |
|
root@www:~# openssl s_client -connect rx-9.srv.world:443 | openssl x509 -noout -startdate -enddate depth=2 C = US, O = Internet Security Research Group, CN = ISRG Root X1 verify return:1 depth=1 C = US, O = Let's Encrypt, CN = R3 verify return:1 depth=0 CN = rx-9.srv.world verify return:1 notBefore=May 10 04:14:04 2022 GMT notAfter=Aug 8 04:14:03 2022 GMT |
|
Matched Content