OKD 4 : Configure Identity Provider : LDAP2022/04/22 |
|
Configure LDAP as an Identity Provider.
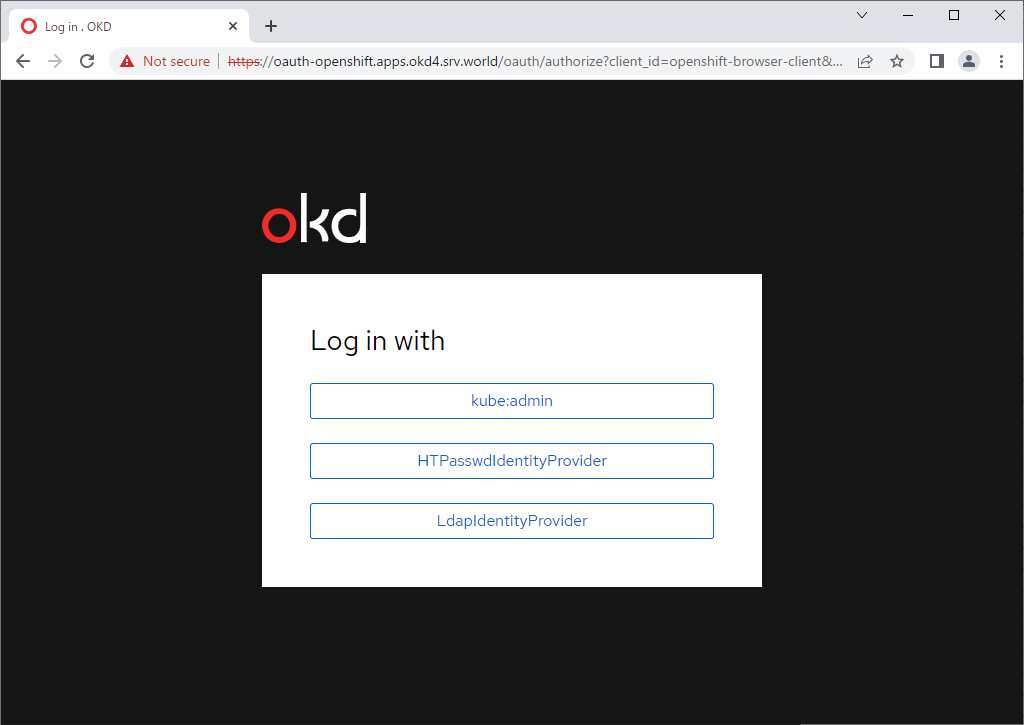
It's possible to set multiple Identity Providers.
Therefore, add LDAP Identity Provider in addition to HTPasswd Identity Provider on this example.
OKD 4 Cluster is based on the environment like follows.
For LDAP server on this example, it uses Windows 2022 Active Directory.
--------------+----------------+-----------------+--------------
|10.0.0.25 | |10.0.0.24
+-------------+-------------+ | +--------------+-------------+
| [mgr.okd4.srv.world] | | | [bootstrap.okd4.srv.world] |
| Manager Node | | | Bootstrap Node |
| DNS | | | |
| Nginx | | | |
+---------------------------+ | +----------------------------+
|
--------------+----------------+-----------------+--------------
|10.0.0.40 | |10.0.0.41
+-------------+-------------+ | +--------------+-------------+
| [master-0.okd4.srv.world] | | | [master-1.okd4.srv.world] |
| Control Plane#1 | | | Control Plane#2 |
| | | | |
| | | | |
+---------------------------+ | +----------------------------+
|
--------------+----------------+-----------------+--------------
|10.0.0.42 |10.0.0.100
+-------------+-------------+ +--------------+-------------+
| [master-2.okd4.srv.world] | | [fd3s.srv.world] |
| Control Plane#3 | | Active Directory |
| | | |
| | | |
+---------------------------+ +----------------------------+
|
| [1] |
Create an user on Active Directory for binding Active Directory from OKD Cluster.
On this example, it creates [ldapuser], it's OK to grant [Domain Users] rights only for it. |
| [2] | On Manager Node, add Identity Provider setting. |
|
# generate LDAP secret # [binduserpass] ⇒ replace to your AD user's password for binding created in [1] [root@mgr ~]# oc create secret generic ldap-secret --from-literal=bindPassword=binduserpass -n openshift-config secret/ldap-secret created
[root@mgr ~]#
oc edit oauth cluster
apiVersion: config.openshift.io/v1
kind: OAuth
metadata:
annotations:
include.release.openshift.io/ibm-cloud-managed: "true"
include.release.openshift.io/self-managed-high-availability: "true"
include.release.openshift.io/single-node-developer: "true"
kubectl.kubernetes.io/last-applied-configuration: |
{"apiVersion":"config.openshift.io/v1","kind":"OAuth","metadata":{"annotations":{},"name":"cluster"},"spec":{"identityProviders":[{"htpasswd":{"fileData":{"name":"htpass-secret"}},"mappingMethod":"claim","name":"HTPasswdIdentityProvider","type":"HTPasswd"}]}}
release.openshift.io/create-only: "true"
creationTimestamp: "2022-08-02T05:37:54Z"
generation: 2
name: cluster
ownerReferences:
- apiVersion: config.openshift.io/v1
kind: ClusterVersion
name: version
uid: d4c7b280-4d13-477d-b271-53f3c0187af6
resourceVersion: "41842"
uid: 047a4c8a-f942-47b1-bc36-38202ffb9ffa
spec:
identityProviders:
- htpasswd:
fileData:
name: htpass-secret
mappingMethod: claim
name: HTPasswdIdentityProvider
type: HTPasswd
- ldap:
attributes:
email:
- mail
id:
- sAMAccountName
name:
- displayName
preferredUsername:
- cn
bindDN: ldapuser@srv.world
bindPassword:
name: ldap-secret
insecure: true
url: >-
ldap://10.0.0.100:389/ou=LDAPUsers,dc=srv,dc=world?sAMAccountName?sub?(objectClass=*)
mappingMethod: claim
name: LdapIdentityProvider
type: LDAP
# add for LDAP binding
# [bindDN] : specify AD user for binding
# [url] : specify LDAP server and search base
# ⇒ example above menas it limits the range to search the directory only [LDAPUsers] OU
# [name] : any name
|
| Get API token if need, refer to here. That's OK if successfully login as an AD user. |
|
|
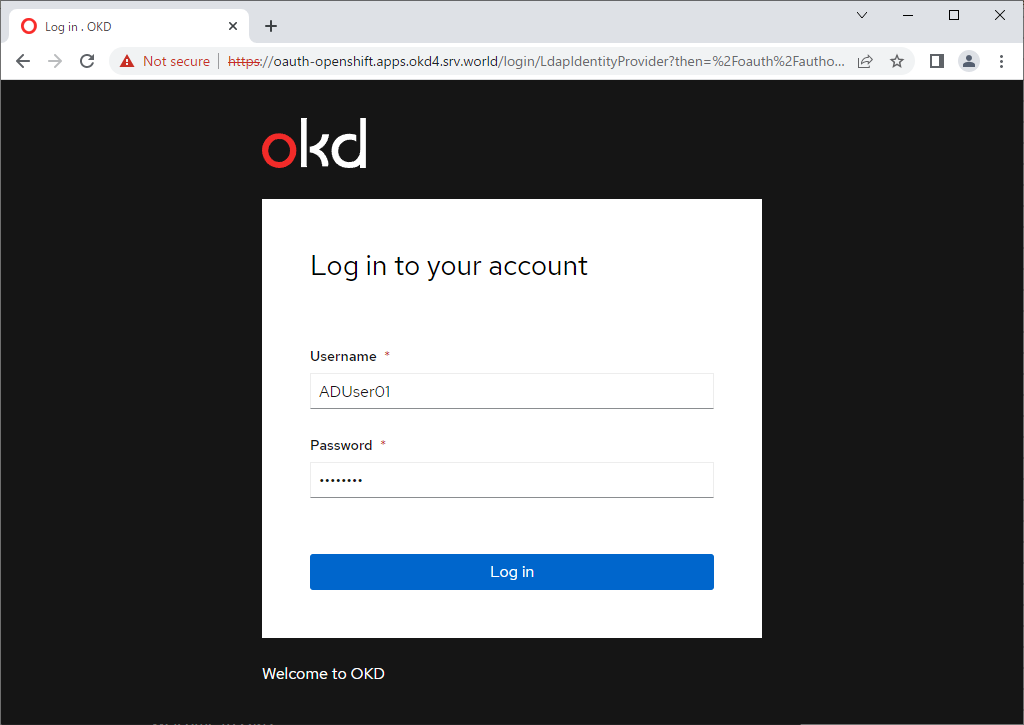
| [3] | Verify on a client computer to login as an AD user. |
|
[centos@client ~]$ oc login -u ADUser01 https://api.okd4.srv.world:6443
The server uses a certificate signed by an unknown authority.
You can bypass the certificate check, but any data you send to the server could be intercepted by others.
Use insecure connections? (y/n): y
Authentication required for https://api.okd4.srv.world:6443 (openshift)
Username: ADUser01
Password:
Login successful.
You don't have any projects. You can try to create a new project, by running
oc new-project <projectname>
Welcome! See 'oc help' to get started.
[centos@client ~]$ oc whoami AD User01 |
Matched Content