FreeIPA : Logon to Windows with FreeIPA User2018/12/26 |
|
Configure to Logon to Windows with FreeIPA User Accounts.
This example is based on the environment like follows. +----------------------+ | +----------------------+ | [ FreeIPA (CentOS) ] |10.0.0.30 | 10.0.0.100| [ Windows (2016) ] | | dlp.ipa.srv.world +----------+-----------+ fd3s.ipa.srv.world | | | | | +----------------------+ +----------------------+ |
| [1] | Add Windows Host on FreeIPA Server and also Get Keytab for Kerberos Principal. |
|
[root@dlp ~]# ipa host-add fd3s.ipa.srv.world --ip-address=10.0.0.100 ------------------------------- Added host "fd3s.ipa.srv.world" ------------------------------- Host name: fd3s.ipa.srv.world Principal name: host/fd3s.ipa.srv.world@IPA.SRV.WORLD Principal alias: host/fd3s.ipa.srv.world@IPA.SRV.WORLD Password: False Keytab: False Managed by: fd3s.ipa.srv.world # ipa-getkeytab -s [FreeIPA Server] -p [Kerberos Principal] -e [Encrypt Type] -k [Keytab File] -P [root@dlp ~]# ipa-getkeytab -s dlp.ipa.srv.world -p host/fd3s.ipa.srv.world -e arcfour-hmac -k /etc/krb5.keytab.fd3s -P
New Principal Password: # set any principal password
Verify Principal Password:
Keytab successfully retrieved and stored in: /etc/krb5.keytab.fd3s
|
| [2] | Configure on Windows. Run Command prompt or PowerShell and execute the commands like follows. > ksetup /setdomain [REALM] > ksetup /addkdc [REALM] [KDC] > ksetup /addkpasswd [REALM] [KDC] > ksetup /setcomputerpassword [PASSWORD] > ksetup /mapuser * * REALM => FreeIPA Server's Realm KDC => Key Distribution Center (on this example, it's FreeIPA Server) |
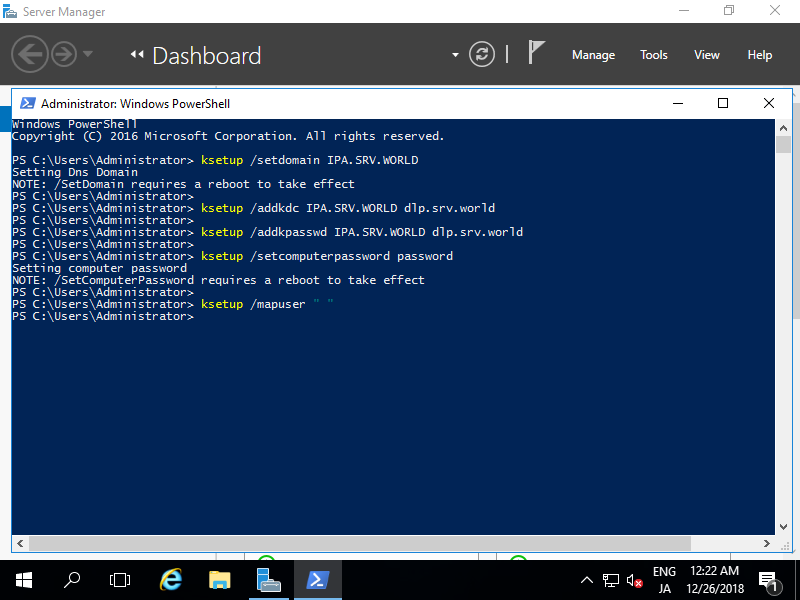
|
| [3] | Next, execute [gpedit.msc] to run GroupPolicy Editor and Click [Windows Settings] - [Security Settings] - [Local Policies] - [Security Options] on left pane and open [Network Security : Configure encryption types allowed for Kerberos]. |
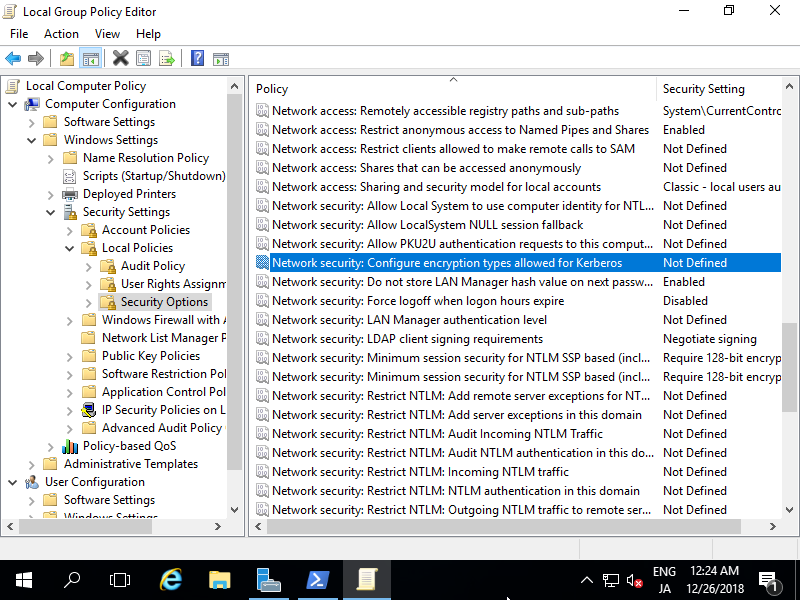
|
| [4] | Check boxes like follows and apply settings. Next, restart the computer. |
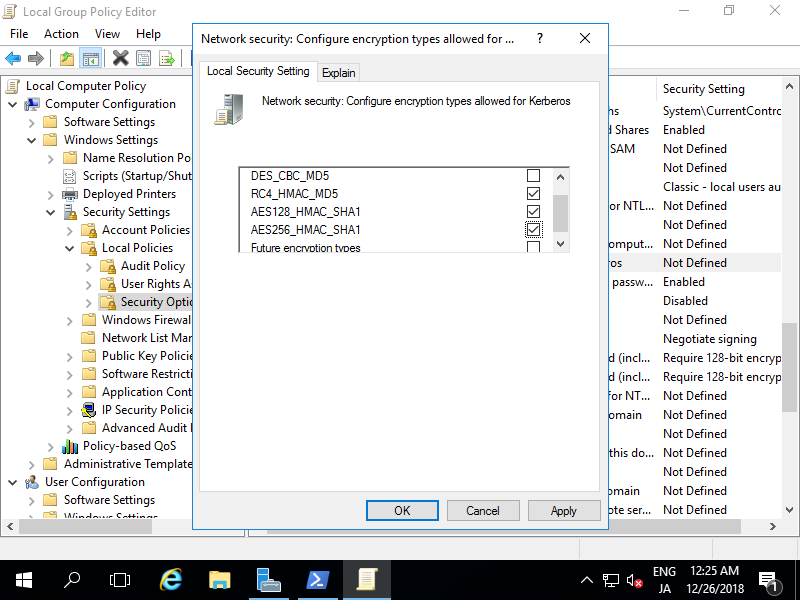
|
| [5] | Create a local user that name is the same with the user on FreeIPA Server for user mapping between FreeIPA and Windows. When logon to Windows, FreeIPA user's password is used, so local Windows user's password is not needed, but if not set local password, it's possible to logon from Console without password, so it had better to prohibit Console logon or set any complicated password with no expire. |
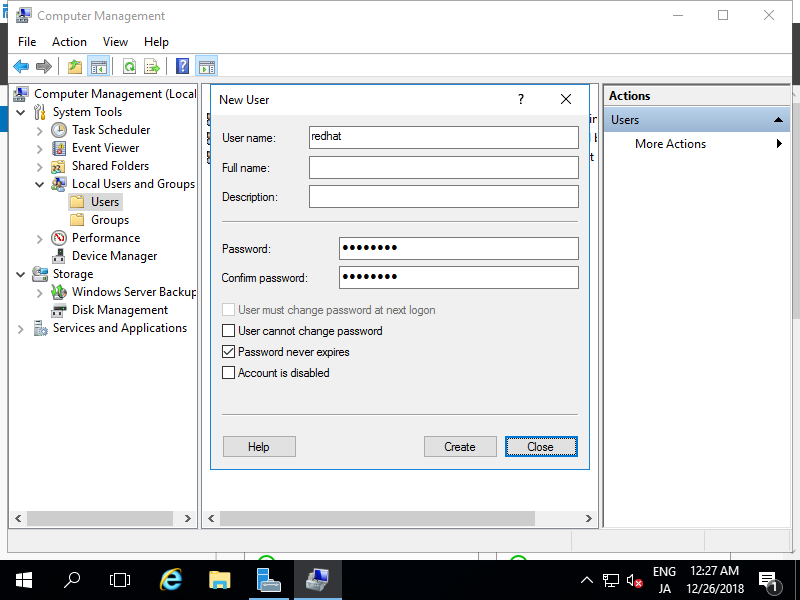
|
| [6] | Logoff and authenticate with a FreeIPA user. |
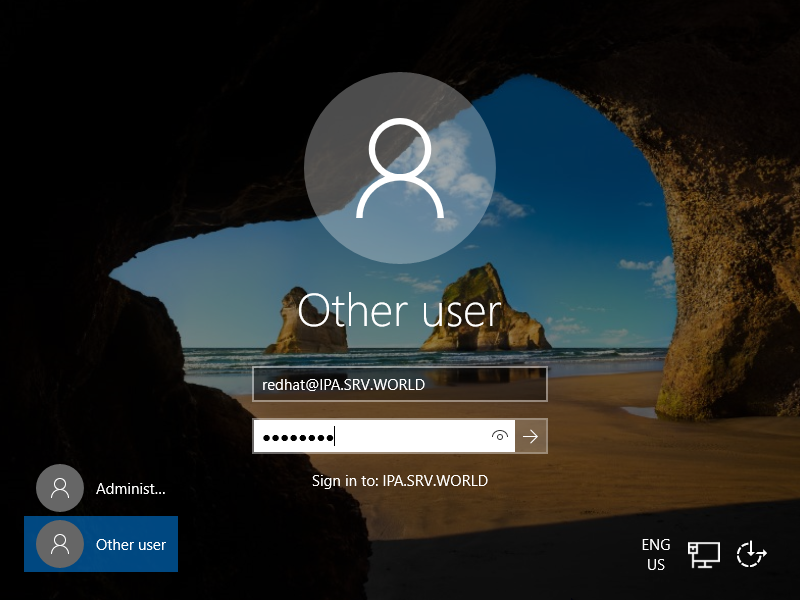
|
| [7] | Just done with FreeIPA user. |
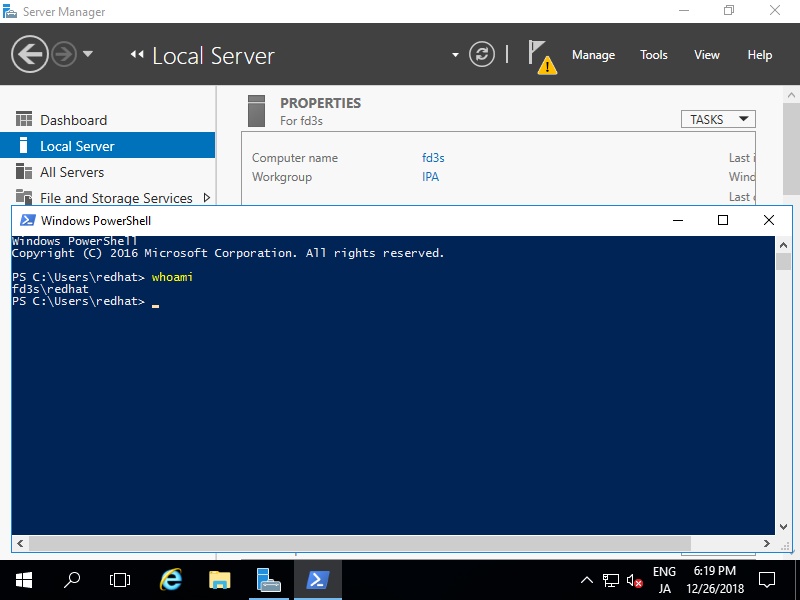
|
Matched Content