Elastic Stack 6 : Configure X-Pack.Security2018/02/25 |
|
Configure X-Pack.Security feature.
|
|
| [1] | Enable X-Pack.Security feature on all Elasticsearch Nodes. And also set password on an Elasticsearch Master Node. |
|
[root@dlp ~]#
vi /etc/elasticsearch/elasticsearch.yml
xpack.license.self_generated.type: trial
xpack.monitoring.enabled: true # enable Security xpack.security.enabled: true xpack.watcher.enabled: false xpack.ml.enabled: false
[root@dlp ~]#
[root@dlp ~]# systemctl restart elasticsearch kibana logstash /usr/share/elasticsearch/bin/x-pack/setup-passwords interactive Initiating the setup of passwords for reserved users elastic,kibana,logstash_system. You will be prompted to enter passwords as the process progresses. Please confirm that you would like to continue [y/N] y # set password on a Master node # even if kibana and logstash is not running, setting password is required Enter password for [elastic]: Reenter password for [elastic]: Enter password for [kibana]: Reenter password for [kibana]: Enter password for [logstash_system]: Reenter password for [logstash_system]: Changed password for user [kibana] Changed password for user [logstash_system] Changed password for user [elastic] |
| [2] | Generate CA and Certificate on an Elasticsearch Master Node which are used among Elasticsearch Nodes in Cluster. |
|
[root@dlp ~]# /usr/share/elasticsearch/bin/x-pack/certutil ca
This tool assists you in the generation of X.509 certificates and certificate
signing requests for use with SSL/TLS in the Elastic stack.
The 'ca' mode generates a new 'certificate authority'
This will create a new X.509 certificate and private key that can be used
to sign certificate when running in 'cert' mode.
Use the 'ca-dn' option if you wish to configure the 'distinguished name'
of the certificate authority
By default the 'ca' mode produces a single PKCS#12 output file which holds:
* The CA certificate
* The CA's private key
If you elect to generate PEM format certificates (the -pem option), then the output will
be a zip file containing individual files for the CA certificate and private key
# specify output file name (if kepp default, Enter with empty)
Please enter the desired output file [elastic-stack-ca.p12]:
# set password
Enter password for elastic-stack-ca.p12 :
# --ca [generated CA file] [root@dlp ~]# /usr/share/elasticsearch/bin/x-pack/certutil cert --ca elastic-stack-ca.p12
This tool assists you in the generation of X.509 certificates and certificate
signing requests for use with SSL/TLS in the Elastic stack.
The 'cert' mode generates X.509 certificate and private keys.
* By default, this generates a single certificate and key for use
on a single instance.
* The '-multiple' option will prompt you to enter details for multiple
instances and will generate a certificate and key for each one
* The '-in' option allows for the certificate generation to be automated by describing
the details of each instance in a YAML file
* An instance is any piece of the Elastic Stack that requires a SSL certificate.
Depending on your configuration, Elasticsearch, Logstash, Kibana, and Beats
may all require a certificate and private key.
* The minimum required value for each instance is a name. This can simply be the
hostname, which will be used as the Common Name of the certificate. A full
distinguished name may also be used.
* A filename value may be required for each instance. This is necessary when the
name would result in an invalid file or directory name. The name provided here
is used as the directory name (within the zip) and the prefix for the key and
certificate files. The filename is required if you are prompted and the name
is not displayed in the prompt.
* IP addresses and DNS names are optional. Multiple values can be specified as a
comma separated string. If no IP addresses or DNS names are provided, you may
disable hostname verification in your SSL configuration.
* All certificates generated by this tool will be signed by a certificate authority (CA).
* The tool can automatically generate a new CA for you, or you can provide your own with the
-ca or -ca-cert command line options.
By default the 'cert' mode produces a single PKCS#12 output file which holds:
* The instance certificate
* The private key for the instance certificate
* The CA certificate
If you elect to generate PEM format certificates (the -pem option), then the output will
be a zip file containing individual files for the instance certificate, the key and the CA certificate
If you elect to generate multiple instances certificates, the output will be a zip file
containing all the generated certificates
# input password of CA you generated
Enter password for CA (elastic-stack-ca.p12) :
# specify output file name (if kepp default, Enter with empty)
Please enter the desired output file [elastic-certificates.p12]:
# set password
Enter password for elastic-certificates.p12 :
Certificates written to /root/elastic-certificates.p12
This file should be properly secured as it contains the private key for
your instance.
This file is a self contained file and can be copied and used 'as is'
For each Elastic product that you wish to configure, you should copy
this '.p12' file to the relevant configuration directory
and then follow the SSL configuration instructions in the product guide.
For client applications, you may only need to copy the CA certificate and
configure the client to trust this certificate.
[root@dlp ~]# chgrp elasticsearch elastic-certificates.p12 elastic-stack-ca.p12 [root@dlp ~]# chmod 640 elastic-certificates.p12 elastic-stack-ca.p12 [root@dlp ~]# mv elastic-certificates.p12 elastic-stack-ca.p12 /etc/elasticsearch/ |
| [3] |
Copy CA and Certificate you generated above to all Elasticsearch Nodes in cluster.
|
| [4] | Configure X-Pack.Security for CA and Certificate on all Elasticsearch Nodes. |
|
# add CA password to keystore [root@dlp ~]# /usr/share/elasticsearch/bin/elasticsearch-keystore add xpack.security.transport.ssl.keystore.secure_password Enter value for xpack.security.transport.ssl.keystore.secure_password: # add Certificate password to keystore [root@dlp ~]# /usr/share/elasticsearch/bin/elasticsearch-keystore add xpack.security.transport.ssl.truststore.secure_password Enter value for xpack.security.transport.ssl.truststore.secure_password:
[root@dlp ~]#
vi /etc/elasticsearch/elasticsearch.yml # add to the end xpack.security.transport.ssl.enabled: true xpack.security.transport.ssl.verification_mode: certificate xpack.security.transport.ssl.keystore.path: /etc/elasticsearch/elastic-certificates.p12 xpack.security.transport.ssl.truststore.path: /etc/elasticsearch/elastic-certificates.p12 systemctl restart elasticsearch |
| [5] | Set SSL Settings that is used on the connection between Elasticsearch Server and Clients. So it needs to get SSL certificates. The environment on this example, there are copied certificates under the [/etc/elasticsearch]. |
|
[root@dlp ~]# chgrp elasticsearch /etc/elasticsearch/*.pem [root@dlp ~]# chmod 640 /etc/elasticsearch/*.pem
[root@dlp ~]#
vi /etc/elasticsearch/elasticsearch.yml # add to the end xpack.security.http.ssl.enabled: true xpack.security.http.ssl.key: /etc/elasticsearch/privkey.pem xpack.security.http.ssl.certificate: /etc/elasticsearch/fullchain.pem
[root@dlp ~]#
systemctl restart elasticsearch
# verify https access : the password is just the one you set on section [1] [root@dlp ~]# curl https://dlp.srv.world:9200/_cat/indices?v -u elastic Enter host password for user 'elastic': health status index uuid pri rep docs.count docs.deleted store.size ... green open .security-6 793s... 1 1 3 0 19.7kb ... green open .monitoring-es-6-2018.03.02 gxG-... 1 1 7725 28 20.3mb ... green open sshd_fail-2018.03 sInv... 5 1 11 0 148.6kb ... green open .monitoring-logstash-6-2018.03.02 31qx... 1 1 164 0 352.1kb ... green open .monitoring-kibana-6-2018.03.02 4WZh... 1 1 11 0 37.1kb ... green open test_index 1vKm... 5 1 1 0 12.2kb ... |
| [6] | If Kibana or Logstash is running, Configure them for Security plugin, too. |
|
[root@dlp ~]#
vi /etc/kibana/kibana.yml # line 21: uncomment and change to https URL elasticsearch.url: " https://dlp.srv.world:9200 "
# line 39: uncomment and change to the username and password you set on section [1] elasticsearch.username: " kibana "elasticsearch.password: " password "
[root@dlp ~]#
systemctl restart kibana
[root@dlp ~]#
vi /etc/logstash/logstash.yml # add to the end # for username and password, they are the one you set on section [1] xpack.monitoring.enabled: true xpack.monitoring.elasticsearch.url: "https://dlp.srv.world:9200/" xpack.monitoring.elasticsearch.username: "logstash_system" xpack.monitoring.elasticsearch.password: "password" xpack.management.enabled: true xpack.management.elasticsearch.url: "https://dlp.srv.world:9200/" xpack.management.elasticsearch.username: "logstash_system" xpack.management.elasticsearch.password: "password" systemctl restart logstash
|
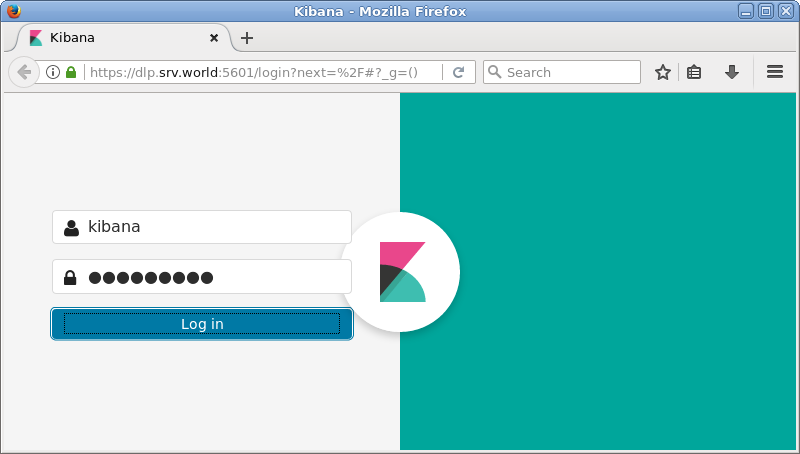
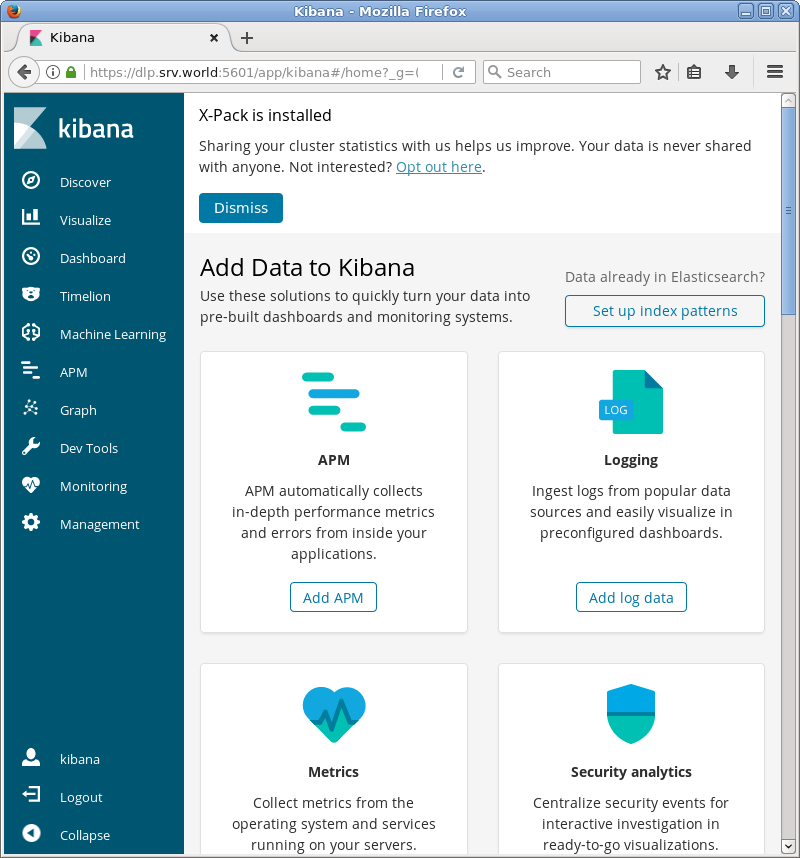
| [7] | Access to Kibana Dashboard, then username and password is required like follows. You can authenticate with them you set on section [1]. |
|
|
Matched Content